Generating Pgp Key File From Server
Aug 17, 2017 And Should we use the same keys for PGP decryption also or it will be a different key for decryption? I believe this is an inbound interface (i.e PI picking file from SFTP server) if yes then you need to generate a separate PGP key pair note the SSH and PGP. In some cases you may need to generate and manage GPG keys on Ubuntu Linux servers or desktops As you may already know, GPG encryption helps keep files save and secure Using GPG encryption to. Pick the file from AL11 - Encrypt it - Place on bank's server 2. Pick the file from Bank's server - Decrypt it - Place on AL11 We are using PGP encryption/Decryption. Bank has already provided their PGP public key. I have uploaded in PGP secure store and used in channel. I am able to encrypt the file. Pgp -export 0x12345678 pgp -export 'Joe User'. You may import a public key from an ASCII Armor file (.asc) or from a text file, the process is the same for both. The file containing the key(s) to be imported must be in the current directory.
- How To Open Key File Icon
- Generating Pgp Key File From Server Free
- .key File Converter
- Generating Pgp Key File From Server Download
Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret, but should be changed for each session. Asymmetric algorithms require the creation of a public key and a private key. Jun 12, 2019 FileZilla is most popular FTP client used by users for connecting FTP server from local system. It has lots of features to use a remote server. But most of them don’t have more idea of how to connect sftp using Filezilla. If you don’t want to use a password, you can simply use SSH private. Jul 01, 2019 The public key, which you share, can be used to verify that the encrypted file actually comes from you and was created using your key. It can also be used by others to encrypt files for you to decrypt. To generate your key pair, open your terminal, and type the following: This will begin the key pair generation.
Introduction
ECN maintains the program gpg for use by faculty, students and staff to enhance security. One of the first duties is to generate a new GPG public and private key. Below is a quick start guide to create your public and private key, then have fellow members sign your public key so that it can be verified.
Generating the public and private keys
In this example, the user cstest will generate the public and private keys, then send his key to the keyserver pgp.mit.edu. Commands you need to type into your machine are bold, underlined, and italicized.
Step 1. Initialize the GPG directory.
If gpg has never been run on cstest's account, then you will need to create a new .gnupg directory is created.
Step 2. Generate a private key
Run the gpg key generation command, and it will actually start to generate a new public and private key pair. Answer the questions as best as you can. I increased the size of the key so that it will last longer (who knows when a new mathematical process will make 1024 bit keys too small). Enter in a really good passphrase (20-25 characters is good, with spaces and punctuation).
That's It! You now have a GPG keypair that you can use for various purposes.
If you are an ECN staffer, you will need to follow the steps outlined below:
Step 3. Get other ECN Staff public keys
Importing other ECN staffer's public keys into your keyring is simple:
Step 4. Send your public key to a keyserver
Keyservers are like synchronized repositories for public keys. A popular one is pgp.mit.edu
Step 5. Keep your keys refreshed, and up to date
battle for middle earth 2 cd key generator. (Optional) Adding other email addresses
And keep going..
In order to build a trusted public key, you need to continue to ask for other peoples' public="" keys,="" sign="" then="" and="" return="" them.="" also="" you="" need="" to="" publish="" your="" key="" so="" others="" can="" find="" it.="" places="" to="" publicly="" make="" your="" key="" available="" are="" on="" your="" home="" web="" page,="" in="" ph,="" or="" a="" key="" server="" like="" the="" one="" at="">
MIT PGP Key Server
Last modified: 2015/06/09 10:26:52.057842 GMT-4 by sundeep.rao.1
Created: 2007/11/06 13:43:16.876000 US/Eastern by brian.r.brinegar.1.
Categories
- Knowledge Base > Security > E-Mail (Security) > GPG
Search
Type in a few keywords describing what information you are looking for in the text box below.
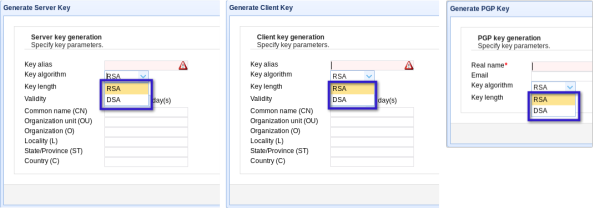
Creating and managing keys is an important part of the cryptographic process. Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret, but should be changed for each session. Asymmetric algorithms require the creation of a public key and a private key. The public key can be made public to anyone, while the private key must known only by the party who will decrypt the data encrypted with the public key. This section describes how to generate and manage keys for both symmetric and asymmetric algorithms.
How To Open Key File Icon
Symmetric Keys
The symmetric encryption classes supplied by the .NET Framework require a key and a new initialization vector (IV) to encrypt and decrypt data. Whenever you create a new instance of one of the managed symmetric cryptographic classes using the parameterless constructor, a new key and IV are automatically created. Anyone that you allow to decrypt your data must possess the same key and IV and use the same algorithm. Generally, a new key and IV should be created for every session, and neither the key nor IV should be stored for use in a later session.
To communicate a symmetric key and IV to a remote party, you would usually encrypt the symmetric key by using asymmetric encryption. Sending the key across an insecure network without encrypting it is unsafe, because anyone who intercepts the key and IV can then decrypt your data. For more information about exchanging data by using encryption, see Creating a Cryptographic Scheme.
The following example shows the creation of a new instance of the TripleDESCryptoServiceProvider class that implements the TripleDES algorithm.
When the previous code is executed, a new key and IV are generated and placed in the Key and IV properties, respectively.
Sometimes you might need to generate multiple keys. In this situation, you can create a new instance of a class that implements a symmetric algorithm and then create a new key and IV by calling the GenerateKey and GenerateIV methods. The following code example illustrates how to create new keys and IVs after a new instance of the symmetric cryptographic class has been made.
When the previous code is executed, a key and IV are generated when the new instance of TripleDESCryptoServiceProvider is made. Another key and IV are created when the GenerateKey and GenerateIV methods are called.
May 05, 2019 Thanks to this fantastic Escape from Tarkov Generator you can generate different Keys for you and your friends!The only Escape from Tarkov code generator that works.No download required.We just released a new leaked Escape from Tarkov Serial Key Generator that can generate keys for Windows PC, Xbox One and Playstation 4.Escape from Tarkov Keygen is a simple-to-use program.  Escape from Tarkov CD Key Generator We present to you the new and updated Escape from Tarkov CD Key Generator. We decide to create this Escape from Tarkov Keygen to help fellow gamers to get a license key and play game for free. There are a lot of online stores now. Escape from Tarkov CD Key Generator Our accomplices frequently offers us an extensive number of free actuation keys which enables us to offer you free permit key each day by means of Escape from Tarkov generator device.Escape from Tarkov CD KEY or Product Key is imperative thing, on the grounds that in the event that you need to play this amusement on the web (multiplayer) at that point you should have.
Escape from Tarkov CD Key Generator We present to you the new and updated Escape from Tarkov CD Key Generator. We decide to create this Escape from Tarkov Keygen to help fellow gamers to get a license key and play game for free. There are a lot of online stores now. Escape from Tarkov CD Key Generator Our accomplices frequently offers us an extensive number of free actuation keys which enables us to offer you free permit key each day by means of Escape from Tarkov generator device.Escape from Tarkov CD KEY or Product Key is imperative thing, on the grounds that in the event that you need to play this amusement on the web (multiplayer) at that point you should have.
Asymmetric Keys
The .NET Framework provides the RSACryptoServiceProvider and DSACryptoServiceProvider classes for asymmetric encryption. These classes create a public/private key pair when you use the parameterless constructor to create a new instance. Asymmetric keys can be either stored for use in multiple sessions or generated for one session only. While the public key can be made generally available, the private key should be closely guarded.
A public/private key pair is generated whenever a new instance of an asymmetric algorithm class is created. After a new instance of the class is created, the key information can be extracted using one of two methods:
The ToXmlString method, which returns an XML representation of the key information.
The ExportParameters method, which returns an RSAParameters structure that holds the key information.
Generating Pgp Key File From Server Free
Both methods accept a Boolean value that indicates whether to return only the public key information or to return both the public-key and the private-key information. An RSACryptoServiceProvider class can be initialized to the value of an RSAParameters structure by using the ImportParameters method.
.key File Converter
Asymmetric private keys should never be stored verbatim or in plain text on the local computer. If you need to store a private key, you should use a key container. For more on how to store a private key in a key container, see How to: Store Asymmetric Keys in a Key Container.
The following code example creates a new instance of the RSACryptoServiceProvider class, creating a public/private key pair, and saves the public key information to an RSAParameters structure.