Asymmetric Function That Generates A New And Separate Key
- Asymmetric Function That Generates A New And Separate Keys
- Asymmetric Function That Generates A New And Separate Key Fob
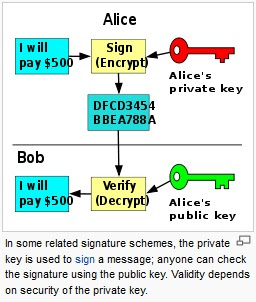
Nov 20, 2014 Asymmetric Encryption. Asymmetric encryption also takes readable data, scrambles it, and unscrambles it again at the other end, but there’s a twist: a different key is used for each end. Encrypters use a public key to scramble the data, and decrypters use the matching private (secret) key on the other end to unscramble it again. If you believe your public key has been used to crack your private key, larger keys and better entropy will result in them taking longer to crack. The current (2012) NIST recommendations for asymmetric keys is to change them every 1-2 years, and to use a minimum key size of 2048 bits. You can use this to acquire a byte array of the appropriate length (e.g. 32 bytes for AES256), which can be used as a key. Be sure to pass in the raw bytes, and not, e.g., a hex-encoded string. Alternatively, you may want to derive a key from some other source. A Key Derivation Function (KDF) is a function that transforms some input into a key. Generating New Cryptographic Keys. Create both asymmetric and symmetric cryptographic keys. However, it’s typically easier to store only the private key and then generate the public key from it when needed. Asymmetric key cryptography is useful because it enables secure communication between two players who don’t share a secret. The password needs to be sufficiently long and sufficiently random that the associated key space of asymmetric keys generated from password data is large enough to withstand brute-force attacks, e.g. In the range of 16 entirely random characters in the set a-z, A-Z, 0-9. RSA asymmetric encryption. RSA is the best known asymmetric (public key) algorithm, named after its inventors: Rivest, Shamir and Adleman. RSA uses public and private keys that are functions of a pair of large prime numbers. Its security is based on the difficulty of factoring large integers.
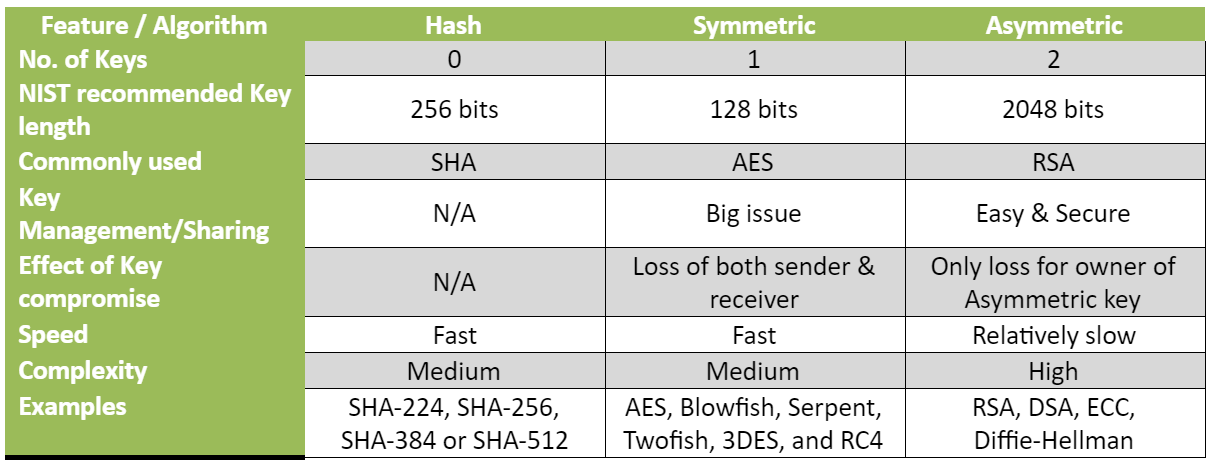
-->Creating and managing keys is an important part of the cryptographic process. Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret, but should be changed for each session. Asymmetric algorithms require the creation of a public key and a private key. The public key can be made public to anyone, while the private key must known only by the party who will decrypt the data encrypted with the public key. This section describes how to generate and manage keys for both symmetric and asymmetric algorithms.
Symmetric Keys
The symmetric encryption classes supplied by the .NET Framework require a key and a new initialization vector (IV) to encrypt and decrypt data. Whenever you create a new instance of one of the managed symmetric cryptographic classes using the parameterless constructor, a new key and IV are automatically created. Anyone that you allow to decrypt your data must possess the same key and IV and use the same algorithm. Generally, a new key and IV should be created for every session, and neither the key nor IV should be stored for use in a later session.
To communicate a symmetric key and IV to a remote party, you would usually encrypt the symmetric key by using asymmetric encryption. Sending the key across an insecure network without encrypting it is unsafe, because anyone who intercepts the key and IV can then decrypt your data. For more information about exchanging data by using encryption, see Creating a Cryptographic Scheme.
The following example shows the creation of a new instance of the TripleDESCryptoServiceProvider class that implements the TripleDES algorithm.
When the previous code is executed, a new key and IV are generated and placed in the Key and IV properties, respectively.
Sometimes you might need to generate multiple keys. In this situation, you can create a new instance of a class that implements a symmetric algorithm and then create a new key and IV by calling the GenerateKey and GenerateIV methods. The following code example illustrates how to create new keys and IVs after a new instance of the symmetric cryptographic class has been made.
When the previous code is executed, a key and IV are generated when the new instance of TripleDESCryptoServiceProvider is made. Another key and IV are created when the GenerateKey and GenerateIV methods are called. Adobe cs4 master collection key generator reddit.
Asymmetric Keys
Asymmetric Function That Generates A New And Separate Keys
The .NET Framework provides the RSACryptoServiceProvider and DSACryptoServiceProvider classes for asymmetric encryption. These classes create a public/private key pair when you use the parameterless constructor to create a new instance. Asymmetric keys can be either stored for use in multiple sessions or generated for one session only. While the public key can be made generally available, the private key should be closely guarded.
A public/private key pair is generated whenever a new instance of an asymmetric algorithm class is created. After a new instance of the class is created, the key information can be extracted using one of two methods:
The ToXmlString method, which returns an XML representation of the key information.
The ExportParameters method, which returns an RSAParameters structure that holds the key information.
Both methods accept a Boolean value that indicates whether to return only the public key information or to return both the public-key and the private-key information. An RSACryptoServiceProvider class can be initialized to the value of an RSAParameters structure by using the ImportParameters method.
Asymmetric Function That Generates A New And Separate Key Fob
Asymmetric private keys should never be stored verbatim or in plain text on the local computer. If you need to store a private key, you should use a key container. For more on how to store a private key in a key container, see How to: Store Asymmetric Keys in a Key Container.
The following code example creates a new instance of the RSACryptoServiceProvider class, creating a public/private key pair, and saves the public key information to an RSAParameters structure.
There is more than one method to do this.The most simple way is to use the ssh-copy-id utility. In order for this to work, you should be able to connect to your server via SSH using password authentication.You can then use the following command to upload the public key to your remote server: ssh-copy-id serverYou will be asked to enter your user password (in our example that would be the root password) and press Enter. After the connection has been established, the contents of the idrsa.pub (the public key) will be copied into the /root/ssh/authorizedkeys file on the remote server.The following output should be displayed: Number of key(s) added: 1Now try logging into the machine, with: 'ssh 'and check to make sure that only the key(s) you wanted were added.From now on, you should now be able to authenticate to your Ubuntu server using your SSH keys. Generate ssh key putty.