Generate Cert And Key Microsoft Ca
Applies to: Configuration Manager (current branch)
Jul 28, 2013 Using a Microsoft CA to generate certificates for Horizon Workspace July 28, 2013 2 Comments During installation of Horizon Workspace in the last post we used self-signed certificates for simplicity but when you will put Workspace in production you will definitely want to replace those certificates. Apr 17, 2018 Creating a key. Open the Microsoft Management Console (MMC) for IIS. In the MMC, expand the Internet Information Server folder by clicking the plus sign (+). Click the plus sign (+) sign next to the computer name. The Default Web Site should be. Oct 16, 2019 The process of creating a trusted certificate involves using a cryptographic tool to generate a private key which is then submitted to a certificate authority (CA), which will in turn generate a certificate. Microsoft offers a MAKECERT utility that is useful for testing but not recommended for production environments. Apr 19, 2018 Select Advanced certificate request Select Create and submit a request to this CA In the Certificate Template, select L2TP/IPSec (Offline request) In the Identifying Information For Offline Template, type the Fully Qualified Domain Name (FQDN) for the non domain member computer in the Name field e.g. Aug 22, 2014 Right click the appropriate CA cert and choose 'All Tasks'- 'Export' The Certificate Export Wizard will launch 9. Click 'Next'- Select 'Yes, Export the private key'- 'Next' 10. Uncheck all of the options here. PKCS 12 should be the only option available. Click 'Next' 11. Give the private key a password of your choice 12. Create a server certificate. Next, you'll create a server certificate using OpenSSL. Create the certificate's key. Use the following command to generate the key for the server certificate. Openssl ecparam -out fabrikam.key -name prime256v1 -genkey Create the CSR (Certificate Signing Request) The CSR is a public key that is given to a CA when requesting a certificate. The CA issues the certificate for this. To generate a Certificate Signing Request (CSR) for Server 2016 – IIS 10 & 10.5 you will need to create a key pair for your server the public key and private key. These two items are a digital certificate key pair and cannot be separated.
Learn how to create a certificate profile that uses a certification authority for credentials. This article highlights specific information about personal information exchange (PFX) certificate profiles. For more information about how to create and configure these profiles, see Certificate profiles.
Configuration Manager allows you to create a PFX certificate profile using credentials issued by a certificate authority. You can choose Microsoft or Entrust as your certificate authority. When deployed to user devices, PFX files generate user-specific certificates to support encrypted data exchange.
To import certificate credentials from existing certificate files, see Import PFX certificate profiles.
Prerequisites
Before you start creating a certificate profile, make sure the necessary prerequisites are ready. For more information, see Prerequisites for certificate profiles. For example, for PFX certificate profiles, you need a certificate registration point site system role.
Create a profile
In the Configuration Manager console, go to the Assets and Compliance workspace, expand Compliance Settings, expand Company Resource Access, and then select Certificate Profiles.
On the Home tab of the ribbon, in the Create group, select Create Certificate Profile.
On the General page of the Create Certificate Profile Wizard, specify the following information:
Name: Enter a unique name for the certificate profile. You can use a maximum of 256 characters.
Description: Provide a description that gives an overview of the certificate profile that helps to identify it in the Configuration Manager console. You can use a maximum of 256 characters.
Select Personal Information Exchange - PKCS #12 (PFX) settings - Create. This option requests a certificate on behalf of a user from a connected on-premises certificate authority (CA). Choose your certificate authority: Microsoft or Entrust Datacard.
Note
The Import option gets information from an existing certificate to create a certificate profile. For more information, see Import PFX certificate profiles.
On the Supported Platforms page, select the OS versions that this certificate profile supports. For more information on supported OS versions for your version of Configuration Manager, see Supported OS versions for clients and devices.
On the Certificate Authorities page, choose the certificate registration point (CRP) to process the PFX certificates: Modern warfare 3 steam charts.
- Primary Site: Choose the server containing the CRP role for the CA.
- Certification authorities: Select the relevant CA.
For more information, see Certificate infrastructure.
The settings on the PFX Certificate page vary depending on the selected CA on the General page:
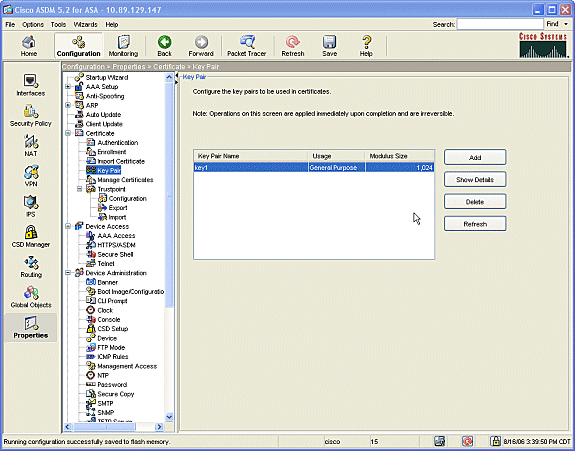
Configure PFX Certificate settings for Microsoft CA
Generate Cert And Key Microsoft Campus
For the Certificate template name, choose the certificate template.
To use the certificate profile for S/MIME signing or encryption, enable Certificate usage.
When you enable this option, it delivers all PFX certificates associated with the target user to all of their devices. If you don't enable this option, each device receives a unique certificate.
Set Subject name format to either Common name or Fully-distinguished name. If you're unsure which one to use, contact your CA administrator.
For the Subject alternative name, enable Email address and User principle name (UPN) as appropriate for your CA.
Renewal threshold: Determines when certificates are automatically renewed, based on the percentage of time remaining before expiration.
Set the Certificate validity period to the lifetime of the certificate.
When the certificate registration point specifies Active Directory credentials, enable Active Directory publishing.
If you selected one or more Windows 10 supported platforms:
Set the Windows certificate store to User. (The Local Computer option doesn't deploy certificates, don't choose it.)
Select one of the following Key Storage Provider (KSP):
- Install to Trusted Platform Module (TPM) if present
- Install to Trusted Platform Module (TPM) otherwise fail
- Install to Windows Hello for Business otherwise fail
- Install to Software Key Storage Provider
Complete the wizard.
Configure PFX Certificate settings for Entrust Datacard CA
For the Digital ID Configuration, choose the configuration profile. The Entrust administrator creates the digital ID configuration options.
To use the certificate profile for S/MIME signing or encryption, enable Certificate usage.
When you enable this option, it delivers all PFX certificates associated with the target user to all of their devices. If you don't enable this option, each device receives a unique certificate.
To map Entrust Subject name format tokens to Configuration Manager fields, select Format.
The Certificate Name Formatting dialog lists the Entrust Digital ID configuration variables. For each Entrust variable, choose the appropriate Configuration Manager fields.
To map Entrust Subject Alternative Name tokens to supported LDAP variables, select Format.
The Certificate Name Formatting dialog lists the Entrust Digital ID configuration variables. For each Entrust variable, choose the appropriate LDAP variable.
Renewal threshold: Determines when certificates are automatically renewed, based on the percentage of time remaining before expiration.
Set the Certificate validity period to the lifetime of the certificate.
When the certificate registration point specifies Active Directory credentials, enable Active Directory publishing.
If you selected one or more Windows 10 supported platforms:
Set the Windows certificate store to User. (The Local Computer option doesn't deploy certificates, don't choose it.)
Select one of the following Key Storage Provider (KSP):
- Install to Trusted Platform Module (TPM) if present
- Install to Trusted Platform Module (TPM) otherwise fail
- Install to Windows Hello for Business otherwise fail
- Install to Software Key Storage Provider
Complete the wizard.
Deploy the profile

After you create a certificate profile, it's now available in the Certificate Profiles node. For more information on how to deploy it, see Deploy resource access profiles.